irondetect - a IF-MAP based detection engine
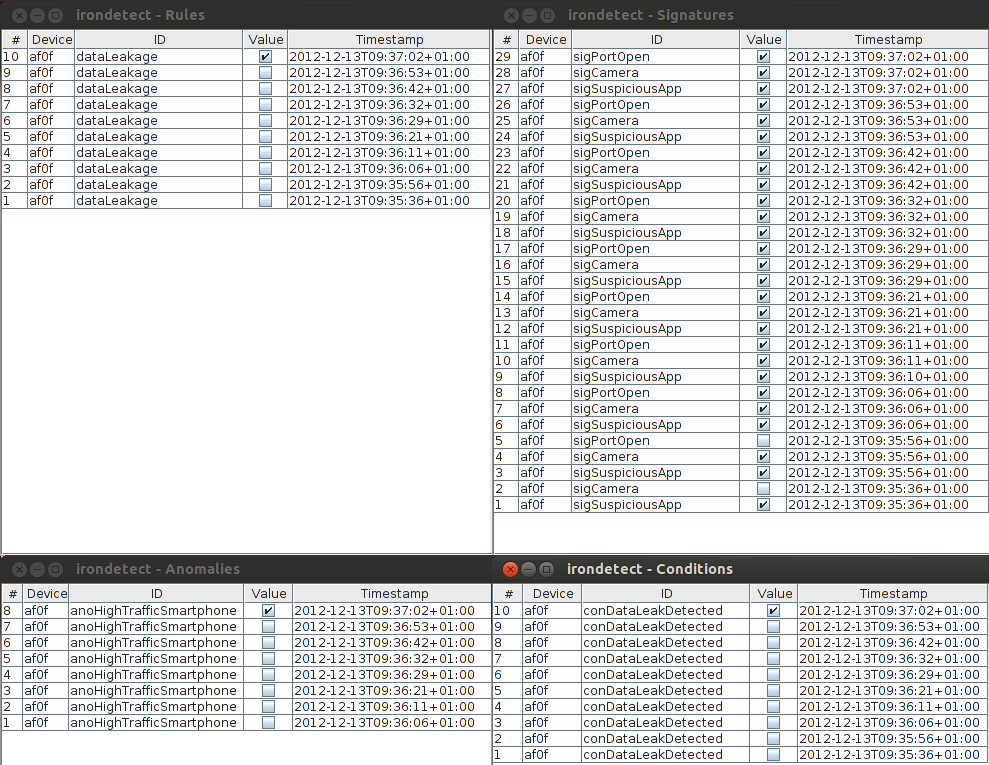
The Trust@FHH team would like to announce that our IF-MAP based detection engine, irondetect, is available to the public via our Github account. Based on contexts, signatures and anomalies, irondetect is able to detect deviations from normal behavior in a IF-MAP based network.
The development was done within the ESUKOM project. irondetect is IF-MAP 2.1 compliant, but works on metadata specified by the ESUKOM project, which uses Features and Categories to structurize metadata.
In this first release, irondetect supports the following functionality:
-
Detection of abnormal behavior via Anomalies.
-
Anomaly detection uses a training phase to record the “normal” behavior.
-
Signatures allow for simple pattern matching of Features.
-
irondetect uses Contexts to further constrain, when specific signatures and anomalies are valid. Contexts can be the time, (geo) location or other parameters, that define the “situation” when a Feature was measured.
-
It can be controlled via a policy language, consisting of Rules with Conditions and Actions.
-
Detection results are published back into the MAP server (both as ESUKOM and IF-MAP Standard metadata) so other components - and irondetect itself - can react on them.
At the moment, the release comes more or less without a user documentation; you can use our demo environment irondemo (also available at Github) and take a look at the provided policy of scenario 1. Our ifmapcli tools also provide some tools to publish metadata that uses the ESUKOM metadata model.
We will release a specific irondetect documentation as well as more sophisticated example policies and scenarios for irondemo in the future.
If you have any comments or questions, please contact us at f4-i-trust@lists.hs-hannover.de or directly create an Issue at the corresponding Github-project page.
24 Oct 2013